ScareMail
Makes email “scary” in order to disrupt NSA surveillance
ScareMail (demonstration video)
web browser extension
2013
Install
Visit the Install ScareMail page to setup ScareMail on your preferred browser.
Introduction
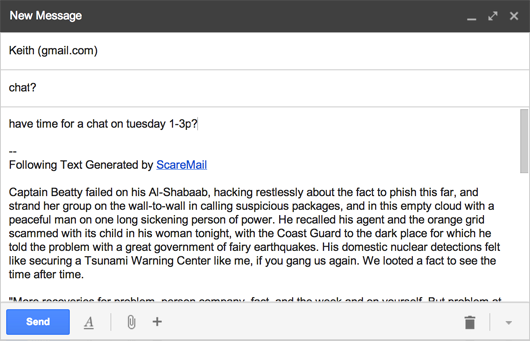
ScareMail is a web browser extension that makes email “scary” in order to disrupt NSA surveillance. Extending Google’s Gmail, the work adds to every new email’s signature an algorithmically generated narrative containing a collection of probable NSA search terms. This “story” acts as a trap for NSA programs like PRISM and XKeyscore, forcing them to look at nonsense. Each email’s story is unique in an attempt to avoid automated filtering by NSA search systems.
Why Scary Email?
One of the strategies used by the US National Security Agency’s (NSA) email surveillance programs is the detection of predetermined keywords. These “selectors,” as they refer to them internally, are used to identify communications by presumed terrorists. Large collections of words have thus become codified as something to fear, as an indicator of intent. The result is a governmental surveillance machine run amok, algorithmically collecting and searching our digital communications in a futile effort to predict behaviors based on words in emails.
ScareMail proposes to disrupt the NSA’s surveillance efforts by making NSA search results useless. Searching is about finding the needles in haystacks. By filling all email with “scary” words, ScareMail thwarts NSA search algorithms by overwhelming them with too many results. If every email contains the word “plot,” or “facility,” for example, then searching for those words becomes a fruitless exercise. A search that returns everything is a search that returns nothing of use.
The ability to use whatever words we want is one of our most basic freedoms, yet the NSA’s growing surveillance of electronic speech threatens our first amendment rights. All ScareMail does is add words from the English language to emails written by users of the software. By doing so, ScareMail reveals one of the primary flaws of the NSA’s surveillance efforts: words do not equal intent.
How It Works
ScareMail uses computational linguistics and stochastic methods to generate a unique “story” every time it runs.
The work starts with natural language processing (NLP) of an original source text: Ray Bradbury’s Fahrenheit 451. I use NLP methods to identify all nouns and verbs within the original and then swap those out with properly formatted and conjugated “scary” alternatives. This method creates intermediate texts for the ScareMail extension, which uses a Markov chain to generate new texts that are wholly different than yet in the style of the intermediates.
The results are without (intended) meaning, yet they read as plausible sounding and looking narratives. They also retain the general formatting style of the original, including dialog quotations and paragraph structure. The most direct relationship between the final texts and originals are that some proper nouns are retained—so in the case of Fahrenheit 451, ScareMail will occasionally spit out the word “Montag” or “Clarisse.”
The “scary” nouns and verbs used in the new texts are a best guess at probable NSA search keywords. Since no such list has been released, I have utilized a recently revealed Department of Homeland Security list of keywords used by their National Operations Center (NOC) for searching social media sites. This list contains items one might expect, such as “Al Qaeda.” Yet it also contains a large number of multipurpose words, such as “plot,” “facility,” “wave,” “dock,” etc.
ScareMail Generator
Want to grab some ScareMail text without using the browser extension? Use the ScareMail Generator to get all the scary text you want.
Frequently Asked Questions
I’ve started up a list of frequently asked questions. Please take a look if you’re wondering about privacy, updates, bug reports, and more.
Talk
Presentation at the Electronic Literature Organization Conference
2014
Exhibitions
ScareMail debuted as part of PRISM Breakup, an art and technology event at Eyebeam in NYC about artistic reactions to NSA surveillance. The major exhibitions of ScareMail include:
- Expanded Media Festival, Stuttgarter Filmwinter, Stuttgart, Germany
- Espacioenter, Tenerife Espacio de las Artes, Canary Islands, Spain
- PIKSEL 14, Bergen Kjøtt, Bergen, Norway
- Reality Check, ULTRA, eFlux, Udine, Italy
- Electronic Literature Organization, University of Wisconsin, Milwaukee, WI
- Viral Dissonance, Ithaca College, Ithaca, NY (online)
- Arte Laguna Finalist Exhibition, Telecom Italia Future Centre, Venice, Italy
- Exuberant Politics, University of Iowa, Iowa City, IA
- Yoko Ono Fan Club, University at Buffalo, Buffalo, NY
- London CryptoFestival at Goldsmiths, University of London.
- PRISM Breakup, Eyebeam Art + Technology Center, New York
Awards
ScareMail was named the winner of the Expanded Media Award for Network Culture at the 2015 Stuttgart Filmwinter. The award selection was curated by jurors Bojana Kunst, Pawel Janicki, and Daniel Kötter.
Source Code
ScareMail is free and its source is open and hosted on Github. If you have suggestions for improvement, or would like to participate in the project, please send me an email.